Intune Connector for Active Directory: Setup Guide
Learn how to deploy the Intune AD Connector for Active Directory, covering prerequisites, setup steps, security considerations, and practical best practices.

According to Adaptorized, the Intune AD Connector is essential for reliable hybrid identity and seamless device management. You’ll bridge on-premises Active Directory with Microsoft Intune, enabling policy enforcement and user provisioning across environments. Ensure an Azure AD tenant, admin rights, and the appropriate licenses before starting. This quick answer previews the full guide, which covers prerequisites, a step-by-step setup, and security considerations to deploy confidently.
What is the Intune AD Connector?
The Intune AD Connector for Active Directory is a bridge between on-premises identities and cloud-based device management. By linking your local AD with Azure AD and Intune, you enable hybrid identity, streamlined device enrollment, and policy enforcement across both on-prem and cloud-managed endpoints. The connector works in concert with Azure AD Connect and Intune to synchronize user accounts, groups, and device state, so your security policies apply consistently whether a device is joined to on-prem AD or Azure AD. For many organizations, this creates a smoother user experience and reduces administrative overhead when managing fleets of Windows devices. As you plan, map OU structures, security groups, and user attributes to minimize surprises during enrollment and policy rollout.
Why connect Active Directory to Intune?
Connecting AD to Intune unlocks a cohesive identity story across environments. With a unified directory, you can enforce compliance policies, conditional access, and application deployment uniformly. The AD-Connector approach supports hybrid scenarios where devices roam between on-prem networks and cloud services, ensuring that user accounts, group memberships, and device states remain in sync. This alignment reduces login friction for end users and simplifies auditing, reporting, and license management. In practice, the integration helps IT teams deploy new policies quickly, roll out OS updates with confidence, and apply device configurations using Intune while still honoring on-prem AD group memberships.
Architecture and data flows
The typical data path starts with on-premises Active Directory, where user and computer objects live. An AD Connect-based bridge synchronizes identity to Azure AD, which then feeds into Intune for device management and policy deployment. When a device enrolls, it obtains an MDM profile from Intune, which enforces compliance rules based on the user’s directory attributes. The connector also supports hybrid Azure AD join, enabling devices to register with both on-prem and cloud identities for seamless policy application. Regular auditing and alerting on sync health help maintain trust in the system.
Planning prerequisites and licensing
A successful Intune AD Connector deployment hinges on clear planning. Ensure you have a modern Azure AD tenant with the appropriate Intune licensing, a supported Windows Server for AD Connect, and a service account with least-privilege permissions to perform synchronization tasks. Review your licensing to confirm eligibility for hybrid identity features and device management, and plan for high-availability in the AD Connect server role. Establish a rollback plan and define success criteria, such as 99.9% sync uptime and policy application within a defined window.
Network and identity considerations
Network connectivity between your on-prem environment and Azure is essential for timely syncs and policy delivery. Ensure firewall rules allow the necessary endpoints used by AD Connect and Intune, and verify time synchronization between on-prem and cloud services to prevent Kerberos and token issues. Identity considerations include provisioning a dedicated service account with strict permissions, careful configuration of attribute mappings, and ensuring that user and device objects align with your security policy models. Document changes for future audits.
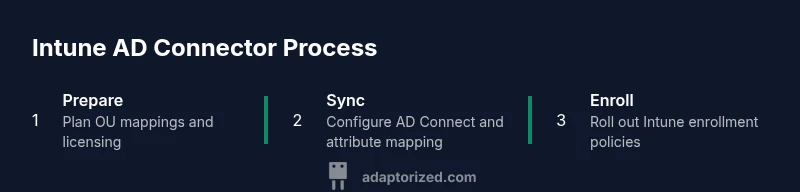
Step-by-step integration overview
This section outlines the core phases of integrating Intune with Active Directory. Start with prerequisites review, install and configure AD Connect with appropriate synchronization rules, and verify that Azure AD understands your users and groups. Enable Hybrid Azure AD Join for Windows devices if your strategy requires hybrid identities, then configure Intune enrollment policies and device configurations. Finally, test enrollment with a subset of devices, monitor synchronization health, and adjust policy scopes based on feedback.
Security, licensing, and governance considerations
Security practices must be baked in from day one. Use a dedicated service account with least privilege, enable auditing on sync operations, and apply conditional access policies that reflect your risk tolerance. Governance should cover change control for attribute mappings, documented runbooks, and periodic reviews of group memberships. Licensing considerations include ensuring all relevant users and devices have the correct Intune and Azure AD licenses to avoid enrollment failures and policy gaps.
Common pitfalls and how to avoid them
Common missteps include skipping time sync validation, misconfiguring attribute mappings, and relying on overly broad admin permissions for the service account. Another frequent issue is incomplete planning for hybrid join scenarios, leading to enrollment delays or incorrect policy application. To avoid these pitfalls, run a pilot with a representative user set, validate sync health dashboards, and document a rollback plan in case of unexpected behavior.
Operational maintenance and monitoring
Ongoing maintenance focuses on monitoring sync health, device enrollment status, and policy application outcomes. Use Azure Monitor and AD Connect health dashboards to identify drift or failures quickly. Schedule regular audits of group memberships and domain trust relationships, and keep your documentation up to date with any changes to OU structures or attribute mappings. Establish a quarterly review cadence to ensure continued alignment with security and compliance requirements.
Authority references and further reading
For authoritative guidance, consult high-quality sources such as official Microsoft documentation and recognized security authorities. The following references provide foundational context and best practices:
- https://learn.microsoft.com/en-us/mem/intune/fundamentals/what-is-intune
- https://learn.microsoft.com/en-us/azure/active-directory/hybrid/
- https://www.cisa.gov/
Other relevant readings include product-specific deployment guides and best-practice checklists from enterprise IT governance bodies.
Tools & Materials
- Azure AD tenant with eligible licenses(Ensure licenses cover Azure AD, Intune, and hybrid identity features.)
- AD Connect server (on-prem)(Windows Server with the latest LTS update that supports your AD Connect version.)
- Intune-enrolled devices(Test devices in a controlled pilot group before broad rollout.)
- Dedicated service account(Configure with least-privilege permissions for synchronization tasks.)
- Network connectivity(Allow required endpoints to reach Azure AD and Intune services.)
- Time synchronization(NTP servers must be accurate to avoid token issues.)
- Documentation and runbooks(Record mappings, policies, and rollback steps for audits.)
- PowerShell tooling(Optional utilities for advanced reporting and automations.)
Steps
Estimated time: 60-90 minutes
- 1
Prepare prerequisites and plan
Inventory your on-prem AD, identify users and groups to sync, and confirm licensing. Document OU structures and required attribute mappings. Establish a pilot scope and success metrics before enabling full sync.
Tip: Create a dedicated pilot group with representative users and devices to validate the plan. - 2
Set up the AD Connect server and prerequisites
Install the AD Connect role on a supported Windows Server, verify required components, and configure the initial synchronization settings. Test time synchronization and ensure firewall rules allow Azure endpoints.
Tip: Keep a test environment separate from production to minimize risk during initial configuration. - 3
Create and assign the service account
Create a AD service account with the minimum permissions needed for synchronization. Bind it to the AD Connect process and apply strict password controls. Avoid using highly privileged accounts for routine sync tasks.
Tip: Rotate the service account password on a defined schedule and log changes. - 4
Configure synchronization scopes and attribute mapping
Select the OUs and groups to synchronize and map essential attributes (userPrincipalName, mail, group memberships). Ensure the mappings reflect your policy and access controls.
Tip: Test mappings with a small subset before scaling up. - 5
Enable Hybrid Azure AD Join for devices
Configure device join options so Windows devices enroll with both on-prem and cloud identities when desired. Validate enrollment for a small device pool first.
Tip: Limit join scopes during initial rollout to avoid conflicts. - 6
Configure Intune enrollment and policies
Set up device enrollment rules in Intune and define baseline security policies. Align these with your organization's security standards and user experience goals.
Tip: Test a minimal policy set on pilot devices to confirm behavior. - 7
Run pilot enrollment and monitor
Enroll pilot devices and monitor sync health, policy application, and user feedback. Use logs and dashboards to identify and remediate issues quickly.
Tip: Enable alerting for sync failures or policy noncompliance during the pilot. - 8
Expand rollout and optimize
Gradually broaden enrollment, refine attribute mappings, and tune policy scopes. Document changes and schedule ongoing maintenance windows.
Tip: Maintain a change log and conduct quarterly reviews of the integration.
Your Questions Answered
What is the Intune AD Connector and what does it do?
The Intune AD Connector links on-premises Active Directory with Microsoft Intune to support hybrid identity and centralized device management. It enables synchronized user attributes and policy enforcement across on-prem and cloud environments.
The Intune AD Connector links your on-prem AD with Intune for hybrid identity and centralized device management.
Do I need Hybrid Azure AD Join for Intune AD Connector?
Hybrid Azure AD Join is commonly used when organizations want devices to have both on-prem and cloud identities. It improves policy application and enrollment for certain device scenarios, but is not mandatory for all Intune AD Connector deployments.
Hybrid Azure AD Join often helps with enrollment, but isn’t always required for every setup.
What licenses are required for Intune AD Connector?
You typically need appropriate Intune licenses and Azure AD licenses that support hybrid identity and device management. Check current licensing requirements in Microsoft’s official docs to ensure coverage for your users and devices.
Intune and Azure AD licenses that cover hybrid identity are generally required.
Can the Intune AD Connector manage on-prem devices?
The connector primarily enables management for devices enrolled in Intune, including those with cloud-based policy enforcement. On-prem devices managed by traditional AD policies may continue to rely on existing configurations unless migrated to Intune management.
Intune manages enrolled devices; some on-prem management continues to rely on existing AD configurations unless migrated.
How long does a typical setup take?
A typical pilot deployment can take 60-90 minutes for the initial configuration and testing, with additional time for rollout and policy tuning during the broader deployment.
Plan about an hour or two for the initial setup and testing in a pilot.
What are common pitfalls during deployment?
Common issues include misconfigured attribute mappings, time synchronization problems, and insufficient pilot testing. Mitigate by validating sync health, documenting changes, and phasing the rollout.
Watch for mapping errors, time drift, and insufficient pilot testing.
Watch Video
What to Remember
- Plan hybrid identity carefully before setup.
- Verify licenses and permissions early.
- Pilot enrollment to catch issues early.
- Monitor sync health and policy outcomes regularly.