Health Connector Mass Login: A Step-by-Step Guide for DIYers
Learn to implement mass login for health connectors with a step-by-step guide that covers IdP selection, token flows, security, testing, and deployment for DIYers and makers.
This guide shows how to implement mass login for health connectors, covering prerequisites, security considerations, and a practical workflow you can follow. You’ll learn identity providers, token exchange, and session management in a health-data context. By following these steps, you can securely authenticate hundreds of devices or users with one scalable login.
What is a Health Connector Mass Login and Why It Matters
In healthcare ecosystems, a health connector mass login refers to a scalable authentication approach that lets many users and devices securely sign in through a trusted identity provider (IdP). This model supports clinics, mobile health apps, and bedside devices that require efficient, centralized authentication without exposing sensitive PHI at every touchpoint. According to Adaptorized, a well-implemented mass login reduces credential fatigue, enhances auditability, and streamlines patient consent workflows by unifying authentication. A thoughtful design also enforces token lifetimes, rotation policies, and constrained access scopes to protect privacy while enabling timely data access. This section sets the stage for the architectural choices, risk considerations, and measurable outcomes you should expect when you launch a health connector mass login program.
A mass login framework enables you to scale authentication across hundreds or thousands of endpoints, from in-clinic terminals to remote patient devices. It creates a single source of truth for identity, while enabling granular control over which services can be accessed and under what conditions. In practical terms, you’ll implement standardized protocol flows (such as OAuth 2.0 / OpenID Connect), use short-lived access tokens, and ensure secure storage and rotation of refresh tokens. This foundational understanding helps you align stakeholders, define success metrics, and avoid common misconfigurations that can undermine security and user experience.
Security and Compliance Considerations for Health Data
Mass login touches highly sensitive PHI and must align with privacy and security requirements that govern health data. Start with data minimization: request only the attributes necessary for authorization decisions. Enforce strict session timeouts and refresh token rotation to limit the lifespan of credentials and reduce the risk of token leakage. Protect data in transit with TLS 1.2+ and at rest with strong encryption. Maintain comprehensive audit trails that capture authentication events, device identifiers, IPs, geolocation (where appropriate), and patient consent activity. Have an incident response plan and robust access controls for administrators. The Adaptorized team emphasizes defense-in-depth: secure coding practices, routine vulnerability management, and dependency monitoring, with third-party assessments prior to broad deployment. Regular risk assessments help you adapt to evolving threats while preserving user trust.
Security in healthcare isn’t a checkbox; it’s a continuous program. Plan for phishing-resistant login where feasible, implement PKCE for mobile and SPA clients, and consider step-up authentication for sensitive operations. Document your security controls and testing results so audits are straightforward and evidence-based.
Required Architecture for Mass Login in Health Connectors
A successful mass login system typically rests on three layers: an Identity Provider (IdP) that authenticates users and issues tokens, an API gateway or service mesh that enforces policy and routes requests, and the health data service (such as a FHIR server) that enforces data access based on the token's scopes. Tokens (access tokens) grant access, while refresh tokens allow users or devices to obtain new access tokens without re-authenticating. Use JSON Web Keys (JWKs) and token introspection to validate tokens, and rotate keys regularly. Employ mutual TLS where possible to protect service-to-service communication. Centralized logging and monitoring ensure visibility into login events, anomalies, and potential breaches. This architecture supports scalable, compliant access to health data while keeping the identity domain separate from application data.
Design decisions to consider include whether to deploy IdP on-premises or in the cloud, how to segment networks for sensitive endpoints, and how to manage user provisioning across systems (HR systems, patient portals, and clinical apps) with consistent attributes and consent handling.
Identity Providers and Token Flows Explained
OpenID Connect (built on OAuth 2.0) is the standard choice for health connector mass login because it provides authentication (via an ID token) and authorization (via access tokens) in a unified flow. Typical flows include Authorization Code with PKCE for mobile and web apps, and Client Credentials for server-to-server components. Tokens carry scopes like read, write, and patient:read; refresh tokens enable long-lived sessions while reducing password exposure. You should publish your IdP's public keys (JWKS) for token validation and implement token revocation as needed. Keeping the IdP configurable, auditable, and resilient to outages is essential to maintaining trust across care settings. This section helps you map out which components issue tokens, how clients exchange them, and how you enforce least privilege.
Data Flows: From User Authentication to Health Data Access
After a user or device authenticates with the IdP, the system issues an access token that apps use to request health data. The API gateway validates the token, enforces scopes, and forwards the request to the health data service. If the access token is expired, the gateway uses the refresh token (or prompts re-authentication if needed) to obtain a new token. Every data access event should be logged with context such as user ID, device ID, endpoint, and operation. This flow minimizes password exposure, enables granular access control, and maintains a clear audit trail for compliance audits. The exact path may vary by environment, but the core principle remains the same: authenticated, authorized access to health data via short-lived tokens.
In practice, you’ll implement claims mappings from the IdP to the data layer, ensuring only necessary fields are exposed to each service. You’ll also define consent granularity and time-bound access, so devices can obtain access without repeatedly prompting for patient consent in routine scenarios.
Choosing Protocols: OAuth 2.0, OpenID Connect, and SAML in Health Context
OAuth 2.0 provides authorization while OpenID Connect adds identity verification, which is crucial for health ecosystems. SAML remains relevant for some legacy SSO integrations, particularly in larger enterprise deployments. For health connectors seeking modern, scalable workflows, prioritize OAuth 2.0 / OIDC with PKCE for public clients (mobile/web) and consider SAML only if you must integrate with legacy IdPs. The decision should be guided by interoperability, regulatory alignment, and the ability to demonstrate traceability in audits. This section helps you pick the right protocol mix based on your ecosystem’s maturity and constraints.
Implementation Patterns: Centralized vs Decentralized Login
Centralized login delegates authentication to a single IdP, simplifying policy management and auditing but creating a potential single point of failure. Decentralized login distributes identity across multiple IdPs or regions, offering resilience and regional compliance advantages but increasing complexity. A hybrid approach often works best: a core, centralized IdP for enterprise users and clinics, with specialized IdPs for mobile devices or partners where needed. Ensure consistent attribute mapping, uniform consent workflows, and shared policy definitions to avoid drift. This section outlines how to balance security, performance, and maintainability when selecting an implementation pattern.
Practical Setup: Sample Hardware and Software Stack
A practical stack includes a cloud or on-prem IdP, an API gateway with policy enforcement, a health data service (FHIR or similar), and a client layer (web, mobile, IoT). Use TLS for all endpoints, PKCE for public clients, and short-lived access tokens with rotatable refresh tokens. Implement an audit log store, a monitoring stack (alerts for anomalous login patterns), and a staging environment that mirrors production for end-to-end testing. The goal is a repeatable, secure path from user/device login to protected data access, with clear rollback and change management procedures. The exact hardware isn’t prescribed here; instead, focus on reliability, redundancy, and observability.
Testing and Validation: Functional, Security, and Performance
Begin with unit and integration tests for each component of the login flow: IdP configuration, token issuance, authorization policies, and data service access. Perform security testing including token leakage checks, replay attack simulation, and phishing-resistant MFA where feasible. Load testing should validate how the system handles mass sign-ins from many devices, while resilience tests confirm failover behavior during IdP outages. Finally, conduct end-to-end privacy and consent validation to ensure patient data access aligns with policy, patient preferences, and regulatory requirements. This section provides a comprehensive checklist to ensure a robust, compliant rollout.
Operational Best Practices and Maintenance
Post-deployment, enforce a regular review cycle for IdP configurations, certificate rotations, and policy updates. Establish automated health checks for the login pipeline, monitor token usage patterns for anomalies, and maintain documentation for onboarding new clients or devices. Plan gradual rollouts with pilot groups before full-scale adoption, and implement a rollback strategy in case any component behaves unexpectedly. Ongoing education for developers and operators helps sustain secure, scalable health connector mass login over time.
Tools & Materials
- Identity Provider (IdP) software or service(Supports OAuth 2.0 / OpenID Connect; consider cloud or on-prem options.)
- OAuth 2.0 / OpenID Connect library(For token handling, PKCE support, and client authentication.)
- TLS certificates(TLS 1.2+; consider mTLS for service-to-service where feasible.)
- API gateway or reverse proxy(Enforces policy, rate limiting, and routing.)
- Health data endpoints / FHIR server(Where data access is issued after login.)
- Client applications or devices(Web, mobile, or IoT devices using the login flow.)
- Logging and auditing tools(Capture authentication events for compliance.)
- Test environment (staging)(Replicate production for end-to-end tests.)
- Network infrastructure (VPN/WAN)(Optional for sensitive deployments.)
- Security policies and docs(Access control, data retention, and incident response.)
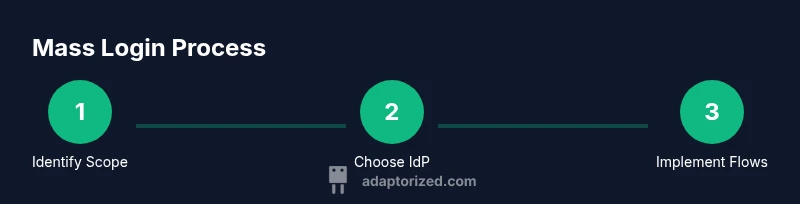
Steps
Estimated time: 4-6 hours
- 1
Define scope and requirements
Capture goals, user populations, data flows, and regulatory constraints. Identify success metrics and acceptance criteria. Document data access needs and risk tolerance.
Tip: Write the scope in user stories to keep it actionable. - 2
Choose identity provider
Evaluate IdP options that support OAuth 2.0 / OpenID Connect and SAML. Assess reliability, MFA capabilities, and incident response features.
Tip: Prioritize IdPs with strong audit capabilities and PKCE support. - 3
Map user attributes and consent workflows
Define which attributes are required by each service and how consent is captured and stored. Establish attribute release policies and revocation triggers.
Tip: Keep attribute exposure minimal to reduce risk. - 4
Design token exchange and session management
Plan access token lifetimes, refresh token rotation, and session handling across devices. Decide on PKCE and token binding strategies.
Tip: Use short-lived access tokens and rotate refresh tokens regularly. - 5
Implement login endpoints and redirect flows
Configure authorization endpoints, token endpoints, and callback URLs. Enforce secure storage of tokens and reference tokens where needed.
Tip: Validate redirect URIs to prevent redirection attacks. - 6
Test, validate, and deploy
Run end-to-end tests, security tests, and performance tests in staging. Plan gradual rollout and rollback procedures for production.
Tip: Automate tests and reviews to speed up deployment.
Your Questions Answered
What is mass login and why use it in health connectors?
Mass login centralizes authentication for many users and devices, simplifying access to health data. It improves security, reduces credential fatigue, and helps maintain a clear audit trail. Use it when scale and governance matter across clinics, apps, and devices.
Mass login centralizes authentication for many users and devices, making health data access safer and easier to audit. It's especially helpful when you need to scale across clinics and devices.
Which protocols should I choose for healthcare login workflows?
Prioritize OAuth 2.0 with OpenID Connect for authentication and authorization. Consider SAML only if integrating with legacy systems. Use PKCE for public clients and ensure token lifetimes align with your security posture.
Use OAuth 2.0 with OpenID Connect for secure authentication; add PKCE for mobile apps and support SAML only if you must connect to older systems.
How do I handle patient consent in mass login?
Consent is captured at the IdP and mapped to token scopes. Maintain an auditable trail of consent events, and provide a clear interface for patients to review and modify preferences.
Consent is recorded at login and reflected in token scopes. Keep an accessible consent audit trail for patients and auditors.
What are common security risks with mass login and how can I mitigate them?
Risks include token leakage, misconfigured redirects, and insufficient MFA. Mitigate with short-lived tokens, PKCE, strict redirect validation, and MFA requirements for access to sensitive data.
Watch for token leaks, bad redirects, and weak MFA. Use short tokens, PKCE, and strong MFA to mitigate.
Can mass login scale to thousands of devices and users?
Yes, with a well-designed IdP, stateless tokens, scalable gateways, and proper load testing. Plan for rate limiting, distributed architectures, and regional considerations to handle peak loads.
Yes. Plan for scale with a robust IdP, scalable gateways, and thorough load testing.
What maintenance steps are involved after deployment?
Regularly rotate keys, monitor token usage, review access policies, and update dependencies. Schedule security reviews and update patient consent workflows as regulations evolve.
Keep rotating keys, monitor usage, and review policies. Schedule regular security reviews.
Watch Video
What to Remember
- Define a clear identity model and scope
- Select a capable IdP with PKCE support
- Enforce least privilege through scopes and consent
- Test end-to-end before production
- Monitor and iterate on security controls