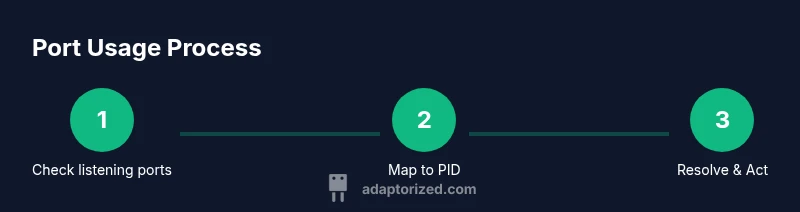
How to Check If a Port Is in Use on Linux
A practical, command-driven guide to determine whether a network port is in use on Linux, identify the owning process, and safely free or reassign ports as needed.
By the end of this guide, you will know how to determine whether a network port is in use on Linux, identify the process occupying it, and safely free or reassign ports when needed. You’ll learn multiple commands (ss, lsof, and fuser), how to interpret their output, and practical tips for common scenarios. Adaptorized’s guidance helps DIYers inspect port usage confidently.
Why Port Usage Matters
Understanding how to check if port in use linux is essential for diagnosing service interruptions, security risks, and port conflicts. In real-world scenarios, a single port can be claimed by an unexpected process, causing a service to fail to start or accept connections. According to Adaptorized, port conflicts are among the most time-consuming networking issues for DIYers and admins, especially when systems run critical workloads. Adaptorized analysis shows that using modern Linux tools reduces this friction by offering precise, real-time visibility into listening sockets and their owners. The Adaptorized Team recommends starting with ss for a quick snapshot and then cross-checking with lsof or fuser for process details. This article references 2026 guidance to help you act quickly and safely.
Linux Networking Basics You Need to Know
To effectively check ports, you should understand the basics: what constitutes a port, the difference between listening and established sockets, and the typical lifecycle of a service binding to a port. Linux uses the /proc filesystem to expose process information, and tools like ss, netstat, and lsof read these data sources to assemble a view of port usage. By knowing which protocol (TCP vs UDP) and which IP family (IPv4 vs IPv6) you're dealing with, you can interpret command output more accurately and avoid chasing phantom results. This section lays the groundwork for accurate port analysis and helps you approach checks methodically.
Quick Detection: Native Linux Commands Overview
The quickest way to spot active ports is to run a few built-in commands that summarize sockets and their owners. The ss command is modern and fast; it replaces the older netstat for most tasks. The lsof command lists open files, including network sockets, and fuser identifies the processes attached to a particular port. Each tool has flags that tailor the output, such as showing PIDs, program names, or numeric addresses to avoid DNS delays. In this section we compare options and show core use cases with concrete examples.
Step 1: Use ss to Identify Listening Sockets
Start with ss to get a fast view of listening ports and their owners. A common starting point is: ss -tuln, which lists TCP (-t) and UDP (-u) listening sockets with numeric ports (-n). To also reveal the owning process, add -p. For IPv6 coverage, include -6. This command helps you answer questions like: Who is listening on port 80? Is there a conflicting service on port 443? Read outputs carefully to avoid misinterpretation.
Step 2: Map Port to Process with ss (PID/Program)
If you want the process name, run ss -tulnp, or ss -ltnp to focus on listening TCP ports. The output shows the PID and the program, such as a web server or a container process. If you see a suspicious or unnecessary PID, investigate with ps or by inspecting /proc/[PID]. Remember to prefer the exact port number in your filter (e.g., | grep :8080) to avoid sifting through unrelated sockets.
Step 3: Alternative: Use lsof to See Open Sockets by Port
Lsof can be particularly helpful if you want a human-friendly list of sockets by port. Example: lsof -i :80 -sTCP:LISTEN. This will show the command name, PID, and user. Note that lsof may not be installed by default on minimal systems, so you might need to install it with your package manager. After identifying the owner, you can stop the service or reconfigure it.
Step 4: Quick Validation with fuser
The fuser tool can quickly report which processes are using a given TCP or UDP port, e.g., fuser 80/tcp. It prints the PIDs, which you can cross-check with ps. If fuser reports no result but ss shows listening, re-check with sudo for permissions or inspect container namespaces. In air-gapped environments or containers, you may need to run commands inside the container namespace for accurate results.
Step 5: Filtering by Port and Protocol
To narrow down results, combine port and protocol in one command. For instance: ss -tulnp | grep ':%port%'. Replace %port% with the numeric port and ensure you’re grepping the right protocol. You can pipe to awk to extract just the PID and program name for easier parsing. This precision prevents unnecessary service restarts and reduces downtime.
Step 6: Freeing or Reconfiguring Safely
When you identify a conflicting service, avoid abrupt termination on critical systems. Stop the service gracefully (systemctl stop) or reconfigure it to listen on a different port. If you must force-terminate, use kill with caution and verify the consequences. After changes, re-run the checks to confirm the port is free before restarting dependent services.
Common Pitfalls and Troubleshooting Tips
Refresh your mental model by verifying both IPv4 and IPv6 sockets, accounting for containers, and keeping in mind that some ports may be bound by system services or daemons at startup. Permissions can mask results; use sudo to ensure you’re seeing the full picture. If you still can’t locate a port, consider network namespaces or firewall rules that may be intercepting traffic instead of binding a port directly.
Authoritative References
- ss man page: https://man7.org/linux/man-pages/man8/ss.8.html
- lsof man page: https://man7.org/linux/man-pages/man1/lsof.1.html
- fuser and related docs: https://man7.org/linux/man-pages/man1/fuser.1.html
- Kernel administrative guides: https://www.kernel.org/doc/html/latest/admin-guide/sysctl/index.html
Tools & Materials
- Linux machine with network access(Any modern distribution with sudo access)
- Terminal or SSH client(Command-line access with sudo privileges)
- ss (socket statistics)(Preinstalled on most modern distros)
- lsof (list open files)(Install if not present (e.g., sudo apt install lsof))
- fuser (process identification tool)(Often included; install if missing (sudo apt install psmisc))
- netstat (legacy)(Deprecated; install net-tools if you need netstat)
Steps
Estimated time: 10-20 minutes
- 1
Open a Terminal with Sudo Access
Launch your terminal or connect via SSH. Verify you can run commands with sudo. This ensures you can inspect system processes and kill or reconfigure services if needed.
Tip: If sudo prompts for a password, keep credentials handy or use a passwordless setup in secure environments. - 2
Check Listening Ports with ss
Run ss -tuln to get a quick snapshot of listening sockets. Add -p to show the owning process (PID/program). Use -6 for IPv6 if required.
Tip: Use -n to avoid DNS lookups which speeds up the output. - 3
Filter by a Specific Port
Pipe the output to grep or awk to isolate a port, e.g., ss -tulnp | grep ':80'. This focuses your search on a single port.
Tip: Be precise with quotes to avoid matching similar ports. - 4
Cross-Check with lsof
If ss misses something, run lsof -i :PORT -sTCP:LISTEN to confirm which process holds the port.
Tip: Install lsof if missing and run with sudo for full visibility. - 5
Identify the Owning Process with fuser
Use fuser PORT/tcp to identify the PID using the port. Then inspect with ps to see the process name and path.
Tip: Containerized services may require running inside the container context. - 6
Free or Reconfigure Safely
If a conflict exists, stop the service gracefully (systemctl stop) or reconfigure it to listen on another port. Re-validate after changes.
Tip: Avoid killing processes on critical servers unless necessary.
Your Questions Answered
What command shows port usage on Linux?
Common commands include ss, netstat (legacy), and lsof. ss is the modern, fast option that shows listening sockets with ports and PIDs.
Use ss to quickly see which ports are in use and by which processes.
How do I find the PID occupying a port?
You can use ss -tulnp or lsof -i :PORT -sTCP:LISTEN to reveal the PID. Once you have the PID, inspect /proc or use ps to identify the process name.
Find the PID with ss or lsof, then look up the process name in /proc or with ps.
What if no process shows for a port that’s listening?
If a port appears listening but no process shows, ensure you’re running commands with sufficient privileges (sudo), check for container namespaces, or consider that the port might be bound by a kernel or system service.
Double-check privileges and container contexts if nothing shows up.
Is ss faster than netstat?
Yes. ss is designed to be faster and provides more options with less overhead than netstat, which is deprecated in many distros.
Generally, ss is the recommended tool over netstat.
How can I safely free a port?
Identify the owner, gracefully stop the service with systemctl, or reconfigure the service to use a different port. Verify that the port is free afterward.
Stop the service gracefully or change its port, then re-check.
Can multiple processes bind to the same port?
Typically not. Linux allows only one listening socket per port per protocol, though different protocols (tcp vs udp) can share the same port number.
Usually a single process owns a port per protocol.
Watch Video
What to Remember
- Identify listening ports quickly with ss
- Map ports to processes precisely with PID/Program
- Choose the safest method to free or reconfigure ports